Thread: Help with NoBugHP
Results 1 to 15 of 17
-
03-17-2022 #1
 Help with NoBugHP
Help with NoBugHP
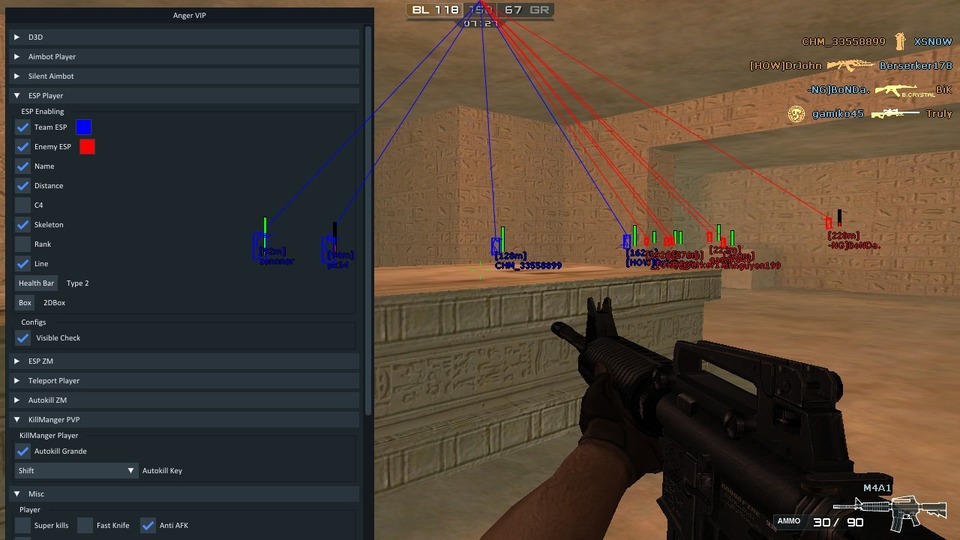
How should I proceed if I found this
https://imgur.com/a/pYyvTlF
But I couldn't find something that would remove the damage in the bugs
I think i need found "loop" when when I go to the address. Right?
https://imgur.com/a/xdx7kOpLast edited by Formula23; 03-17-2022 at 08:17 AM.
-
03-17-2022 #2
-
The Following User Says Thank You to Anger5K For This Useful Post:
Formula23 (03-17-2022)
-
03-17-2022 #3
I didn't know I'm sorry
'I have a cheat on my hands and this function works there, so there is another way?'
and....
I can't find it can you please explain to me how, pleaseCode:CPointers::get()->Bypass_31_0[0] = CShell + 0x00; // \x48\x8B\xF8\x48\x85\xC0\x0F\x84\x00\x00\x00\x00\xC7\x45\xA8\x01\x00\x00\x00, xxxxxxxx????xxxxxxx CPointers::get()->Bypass_31_0[1] = CShell + 0x00; // FE 47 21 Bypass_31_0(0) = jz = JMP 6 Bypass_31_0(1) = nop = 3

Last edited by Formula23; 03-17-2022 at 02:11 PM.
-
03-19-2022 #4
-
03-19-2022 #5CFPH Address/OffsetsCode:
uint64_t m_CZoneManMgr = 0x2293310; uint64_t m_NoBugDamage = 0x2FC;
-
03-19-2022 #6
-
03-19-2022 #7
-
03-19-2022 #8try this pattern if workCode:
NetVars::get()->Pointer.m_CZoneManMgr = NetVarManager::get()->GetOffset(xorstr_(_T("m_CZoneManMgr")), eCShell, (BYTE*)"\x48\x89\x05\x00\x00\x00\x00\x48\x8B\x8A\x00\x00\x00\x00", "xxx????xxx????", 3, false, 0, 7); NetVars::get()->Offset.m_NoBugDamage = NetVarManager::get()->GetOffset(xorstr_(_T("m_NoBugDamage")), eCShell, (BYTE*)"\x88\x87\x00\x00\x00\x00\x89\x9F\x00\x00\x00\x00\x33\xD2", "xx????xx????xx", 2, true);
-
The Following User Says Thank You to MemoryThePast For This Useful Post:
Formula23 (03-20-2022)
-
03-20-2022 #9
-
03-20-2022 #10
Help me
could someone make a file for CrossFire Brazil?
-
03-20-2022 #11
-
03-21-2022 #12
-
03-21-2022 #13
-
03-24-2022 #14
for ru cf
<cshell_x64.dll>+437A888
screen: https://imgur.com/a/VtLWfiA
and just below ( + 2FC )
screen: https://imgur.com/a/Vf50T7u
-
The Following User Says Thank You to freshall For This Useful Post:
Formula23 (03-24-2022)
-
03-24-2022 #15
Similar Threads
-
[Help Request] Need help with numpad while recording macro !
By JonathanTBM in forum Vindictus HelpReplies: 2Last Post: 05-10-2011, 07:37 PM -
[Help Request] help with ca hacks
By moises8 in forum Combat Arms HelpReplies: 4Last Post: 05-10-2011, 05:55 PM -
[Help Request] Anyone can help with this ?
By devileyebg in forum Vindictus HelpReplies: 1Last Post: 05-01-2011, 03:57 PM -
[Help Request] need help with mod
By .:MUS1CFR34K:. in forum Call of Duty Modern Warfare 2 GSC Modding Help/DiscussionReplies: 4Last Post: 05-01-2011, 12:40 PM -
[Help Request] need help with modding
By BayBee Alyn in forum Combat Arms HelpReplies: 0Last Post: 04-27-2011, 09:06 PM


 General
General






 Reply With Quote
Reply With Quote








 how
how 